Open PostgreSQL
Determine if TCP port 5432 for PostgreSQL is open to the public
While some ports such as HTTP and HTTPS are required to be open to the public to function properly, more sensitive services such as PostgreSQL should be restricted to known IP addresses.
Recommended Actions
Follow the appropriate remediation steps below to resolve the issue.
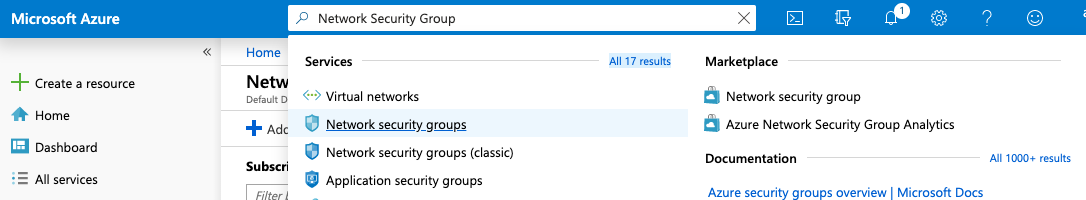
Log into the Microsoft Azure Management Console.
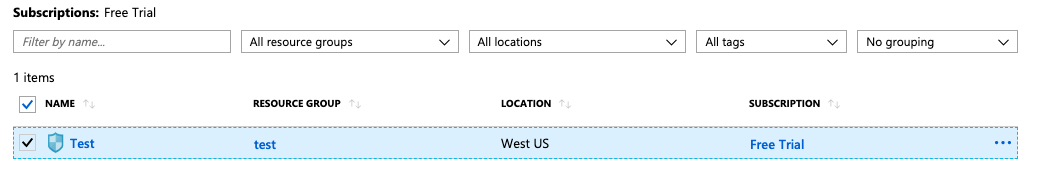
Select the “Search resources, services, and docs” option at the top and search for Network security groups.
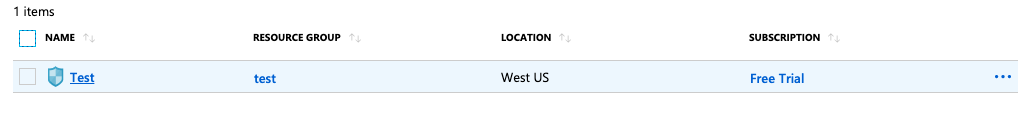
Select the “Network security group” that needs to be verified.
Click on the “Name” of the selected “Network security group” to access the port configurations.
In the “Overview” tab scroll down the page and check the “Inbound security rules.”
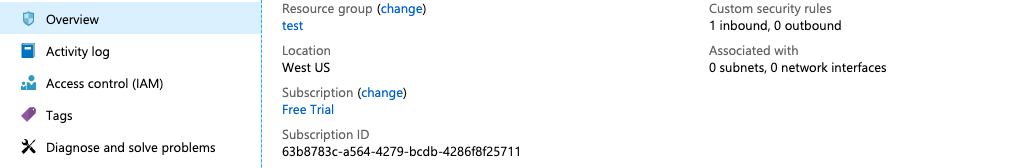
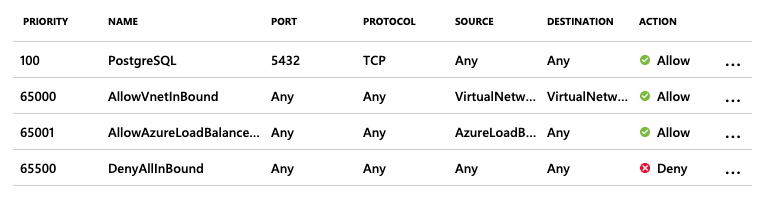
If the “PostgreSQL” for port 5432 with the protocol “TCP” is showing as “Allow” for all “Source” and “Destination” then the selected “Network security group” has TCP port 5432 for PostgreSQL is open to the public.
Repeat steps number 2 - 6 to verify other “Network security group.”
Navigate to the “Network security group” and select the security group that needs to modify for restricting the “TCP” port for “PostgreSQL” on port 5432 to specific IP Address.
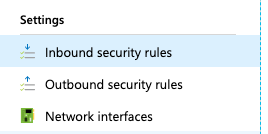
Scroll down the left navigation panel and choose “Inbound security rules” under “Settings.”
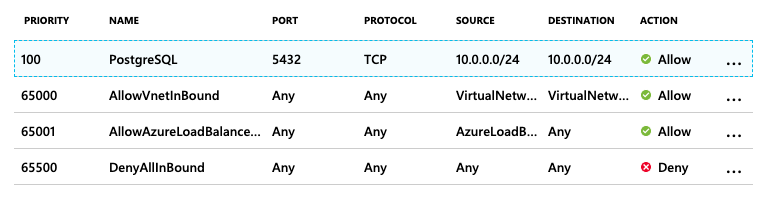
Click on the “PostgreSQL” protocol in the “Name” column and under “Source” select the “IP Address” from the dropdown menu and enter the “Source IP addresses/CIDR ranges” as per the requirement and click on the “Save” option at the top panel.
Repeat steps number 8 - 10 to restrict TCP port 5432 for PostgreSQL to known IP addresses.